Categorie | Security

john (John the Ripper) — a password cracker for Linux and Windows
John the Ripper (a.k.a. JtR, or simply john) is a popular fast password cracker for both Linux and Windows . It is quite useful for identifying weak passwords. By weak, I mean ones that do not take a long time to crack. In this article I will show you how to...

Spyware-ul o realitate. Concurenta pentru retele sociale. Datele tale sunt miza.
Spyware-ul este un malware care se refera la un program rau intentionat sau cod rau intentionat, al carui obiectiv este sa intre intr-un computer sau dispozitiv si sa il deterioreze, toate acestea fara autorizarea proprietarului acestuia. Daca credeai ca doar...

Spyware a reality. Competition for social networks. Your data is at stake.
Spyware is malware that refers to a malicious program or malicious code, the purpose of which is to enter a computer or device and damage it, all without the permission of its owner. If you thought that only social networks would use your personal data to the limit...

Ce este Federated Learning of Cohorts (FLoC)? Este o tehnologie daunatoare?
Timp de doua decenii, cookie-urile (poate partea cea mai gresita a internetului) au fost punctul central al industriei publicitatii de pe web, in valori de multe miliarde de dolari. Amprentele digitale sunt dificil de oprit. Unul, daca nu cumva cel mai important...

What is Federated Learning of Cohorts (FLoC)? Is it a harmful technology?
For two decades, cookies (perhaps the worst part of the Internet) have been the focal point of the web advertising industry, worth billions of dollars. Fingerprints are difficult to stop. One, if not the most important of the colossi of the online...

Testarea securitatatii sistemului - Sometimes, it feels like being watched... Even in my dreams...
Majoritatea spargerilor de sisteme au ca faza initiala adunarea de informatie precum si testarea sistemului de securitate a retelei. Desigur, nu si in cazul in care ati scos o "super" programa de pe Net care "e de ajuns sa...

Testing system security - Sometimes, it feels like being watched ... Even in my dreams ...
Most system breaches have as their initial stage the gathering of information as well as the testing of the network security system. Of course, not if you removed a "super" program from the Net that "just press a button" to break...

Mesaje din rootkit-urile romanesti vechi - ce vremuri .....
Din arhiva de aur. Mesaje din rootkit-urile romanesti echo "Na treaba e facuta mah, acum conecteazate... hihi." echo "[=] All Done Sire ----------->:) l-am smenuit si pe asta !" echo "BadBoys spune sa treci la alt r00t,...

Tools for securing the Linux system
I found a list of programs and web page addresses that deal with network security. So I decided to write this article that aims to help network administrators and not only to have a server as secure as possible. I will start with a list of programs and various security tools that are...

Instrumente pentru securizarea sistemului Linux
Am gasit o lista cu programe si adrese de pagini de Web care se ocupa cu securitatea retelelor. Asa ca m-am hotarat sa scriu acest articol care isi propune ii ajute pe administratorii de retea si nu numai sa aiba un server cat mai sigur. Voi incepe cu o enumerare a...

Lansarile PHP vor fi suspendate timp de doua saptamani din motive de securitate
Echipa PHP a anuntat ca duminica trecuta, atacatori au reusit sa aiba acces la serverul sau principal Git, incarcând doua comiteri rau intentionate (ce pretindeau ca remediaza o "greseala de scriere” in codul sursa), inclusiv un backdoor....

PHP launches will be suspended for two weeks for security reasons
Team PHP announced last Sunday, attackers were able to access the server or main Git uploading two commit malicious (claiming to remedy a "typo" in the source code), including a backdoor. These commissions were immediately observed and canceled and thus...

Integrare ROSA Virtualization 2.0 si Kaspersky Endpoint Security for Business
Kaspersky Endpoint Security for Business, instrument de protectie pentru platforma rusa de gestionare a mediului de virtualizare ROSA Virtualization 2.0. Kaspersky Endpoint Security for Business va ajuta utilizatorii ROSA Virtualization 2.0...

Integration of ROSA Virtualization 2.0 and Kaspersky Endpoint Security for Business
Kaspersky Endpoint Security for Business, protection tool for the Russian virtualization environment management platform ROSA Virtualization 2.0. Kaspersky Endpoint Security for Business will help ROSA Virtualization 2.0 users effectively...
Daca rulati Linux, ar trebui sa actualizati sudo acum
Cei de la Qualys au dezvaluit un nou vector de atac de depasire a bufferului bazat pe heap, care vizeaza programul „sudo” pentru a obtine acces root. Bug-ul exista de aproape 10 ani ! CVE-2021-3156 - Learn...
If you are running Linux, you should update sudo now
Qualys has unveiled a new heap-based buffer override attack vector, which targets the "sudo" program to gain root access. The bug has been around for almost 10 years! CVE-2021-3156 - Learn more at National Vulnerability...

Zephyr Security Update - AMNESIA: 33
On December 8, 2020, Forescout released a report containing numerous vulnerabilities found in various embedded TCP / IP stacks, known as AMNESIA: 33. AMNESIA: 33 is a set of 33 vulnerabilities that impact four open source TCP /

Actualizare de securitate Zephyr - AMNESIA: 33
Pe 8 decembrie 2020, Forescout a lansat un raport care contine numeroase vulnerabilitati gasite in diferite stive TCP / IP incorporate, cunoscut sub numele de AMNESIA: 33 . AMNESIA: 33 este un set de 33 de...

ROSA lanseaza un kit de distributie live ROSA Enterprise Desktop Barium 5 cu protectie criptografica...
ROSA BARIUM este un dispozitiv unic care combina toate functionalitatile instrumentului de protectie criptografica certificata Rutoken EDS 2.0 cu memoria Flash gestionata integrata cu sistemul ROSA BARIUM OS...

ROSA launches a live distribution kit ROSA Enterprise Desktop Barium 5 with Rutoken EDS 2.0 certifie...
ROSA BARIUM is a unique device that combines all the functionalities of the Rutoken EDS 2.0 certified cryptographic protection tool with the managed Flash memory integrated with the installed ROSA BARIUM OS...

Sfaturi pentru imbunatatirea securitatii in Linux
Sistemele de operare bazate pe Linux sunt, dupa opinia specialistilor, medii extrem de sigure pentru utilizatori. Din acest motiv, Linux-ul ruleaza pe cele mai performante computere ale lumii, pe enorma majoritate a serverelor, pe computerele de pe Statia Spatiala internationala...

Tips for improving security in Linux
Linux-based operating systems are, in the opinion of specialists, extremely safe environments for users. For this reason, Linux runs on the most powerful computers in the world, on the vast majority of servers, on computers on the International Space Station, etc., being also in the service of various...

Care sunt simptomele unei tablete sau al unui telefon virusat?
Nu conteaza ca tableta sau telefonul tau inteligent ruleaza Android sau Windows, oricând si oriunde virusii iti pot compromite sistemul si te pot lasa cu datorii financiare imense, stres si pagube la capitolul imagine. De obicei, atunci când esti mai sigur pe tine...

What are the symptoms of a tablet or a infected phone?
It doesn't matter that your tablet or smartphone is running Android or Windows, anytime and anywhere viruses can compromise your system and leave you with huge financial debts, stress and image damage. Usually, when you are more confident or the world is dearer to you, you suffer...
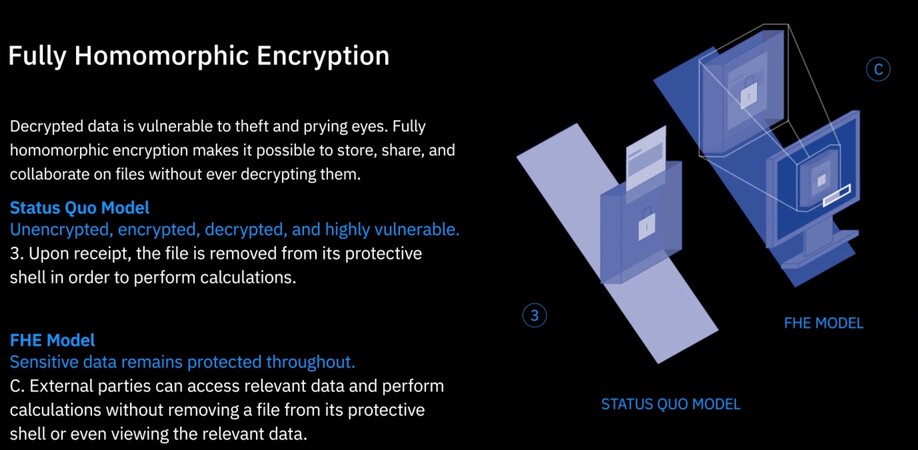
The IBM Fully Homomorphic Encryption Toolkit is available for Linux
After becoming available a few weeks ago for macOS, iOS and Android, the IBM Fully Homomorphic Encryption Toolkit can now be installed on various Linux distributions, including Ubuntu, Fedora and CentOS. According to IBM, FHE (Fully Homomorphic...
 + Add to Google News
+ Add to Google News